Dear College of Education,
As millions of shoppers begin looking for great deals this holiday season, the Education IT team wants to remind everyone to be on the lookout for scams, phishing schemes, and malware. Below are a couple of articles that touch on the subject. Be alert and have a restful and enjoyable holiday season!
–Education IT
—
Cyber Monday: Beware the malware
http://news.cnet.com/8301-27080_3-20023728-245.html
Scammers are ready for unsuspecting online shoppers to be hunting for holiday bargains that hit on what has become known as Cyber Monday (given that more than 40 percent of you will be buying holiday gifts online, according to this survey). There will no doubt be malware hiding on retail sites, fake sites created just for distributing viruses and Trojans, and e-mails with malware-laden attachments and links leading to nastiness…
See: http://news.cnet.com/8301-27080_3-20023728-245.html
—
Holiday Season Phishing Scams and Malware Campaigns
http://www.us-cert.gov/current
added to us-cert.gov on November 18, 2010 at 02:17 pm
In the past, US-CERT has received reports of an increased number of phishing scams and malware campaigns that take advantage of the winter holiday and holiday shopping season. US-CERT reminds users to remain cautious when receiving unsolicited email messages that could be part of a potential phishing scam or malware campaign.
These phishing scams and malware campaigns may include but are not limited to the following:
- electronic greeting cards that may contain malware
- requests for charitable contributions that may be phishing scams and may originate from illegitimate sources claiming to be charities
- screensavers or other forms of media that may contain malware
- credit card applications that may be phishing scams or identity theft attempts
- online shopping advertisements that may be phishing scams or identity theft attempts from bogus retailers
US-CERT encourages users and administrators to use caution when encountering these types of email messages and take the following preventative measures to protect themselves from phishing scams and malware campaigns:
- Do not follow unsolicited web links in email messages.
- Use caution when opening email attachments. Refer to the Using Caution with Email Attachments Cyber Security Tip for more information on safely handling email attachments.
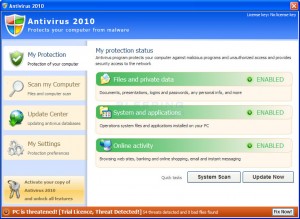
- Maintain up-to-date antivirus software.
- Review the Federal Trade Commission’s Charity Checklist.
- Verify charity authenticity through a trusted contact number. Trusted contact information can be found on the Better Business Bureau National Charity Report Index.
- Refer to the Recognizing and Avoiding Email Scams (pdf) document for more information on avoiding email scams.
- Refer to the Avoiding Social Engineering and Phishing Attacks Cyber Security Tip for more information on social engineering attacks.
- Refer to the Shopping Safely Online Cyber Security Tip for more information on online shopping safety.